Symantec Protection identifies Process Hacker as a risk · Issue #388 · winsiderss/systeminformer · GitHub

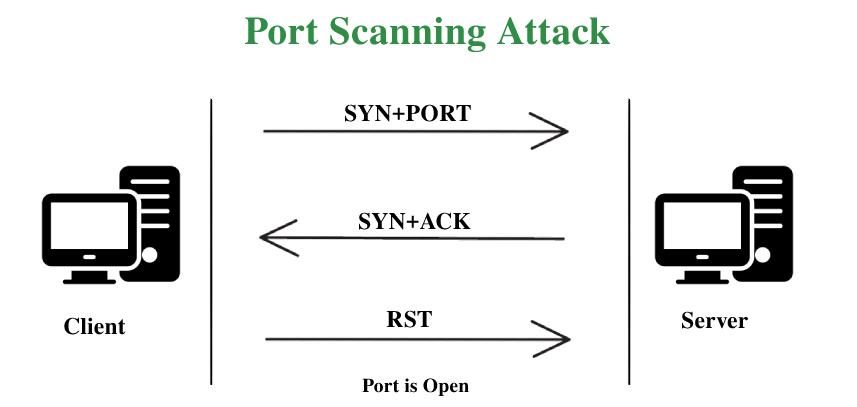
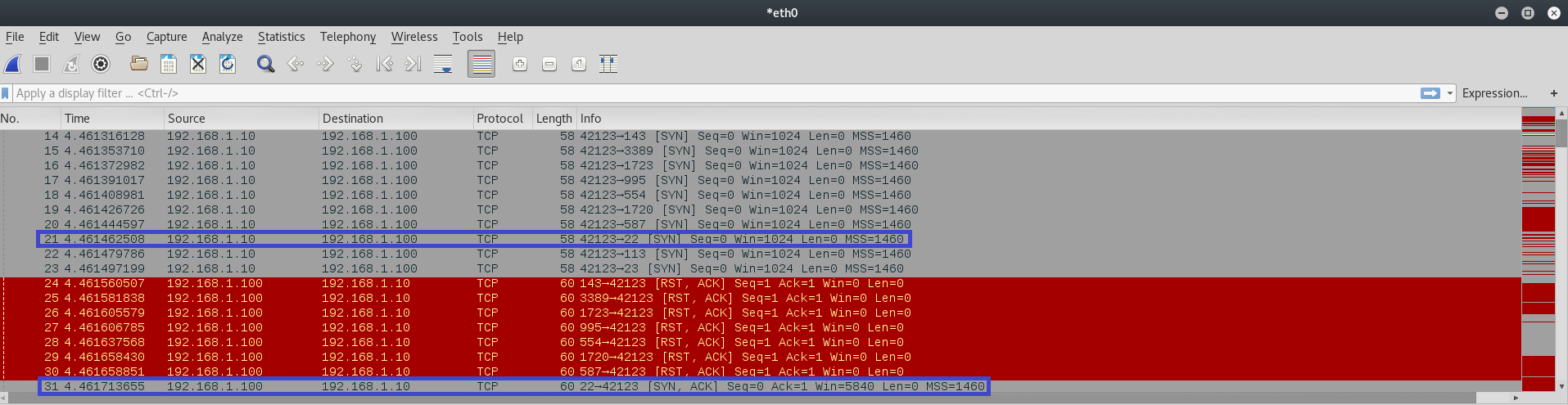
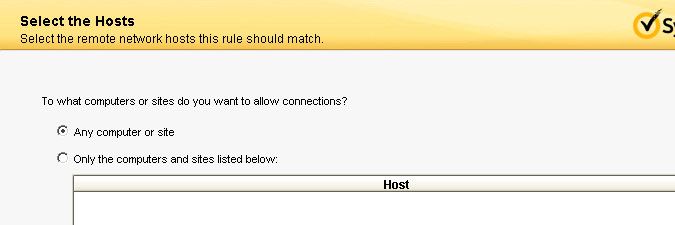
How to exclude an IP (Vulnerability Scanner) from being detected as a port scan | Endpoint Protection

Novel intrusion prediction mechanism based on honeypot log similarity - Jiang - 2016 - International Journal of Network Management - Wiley Online Library
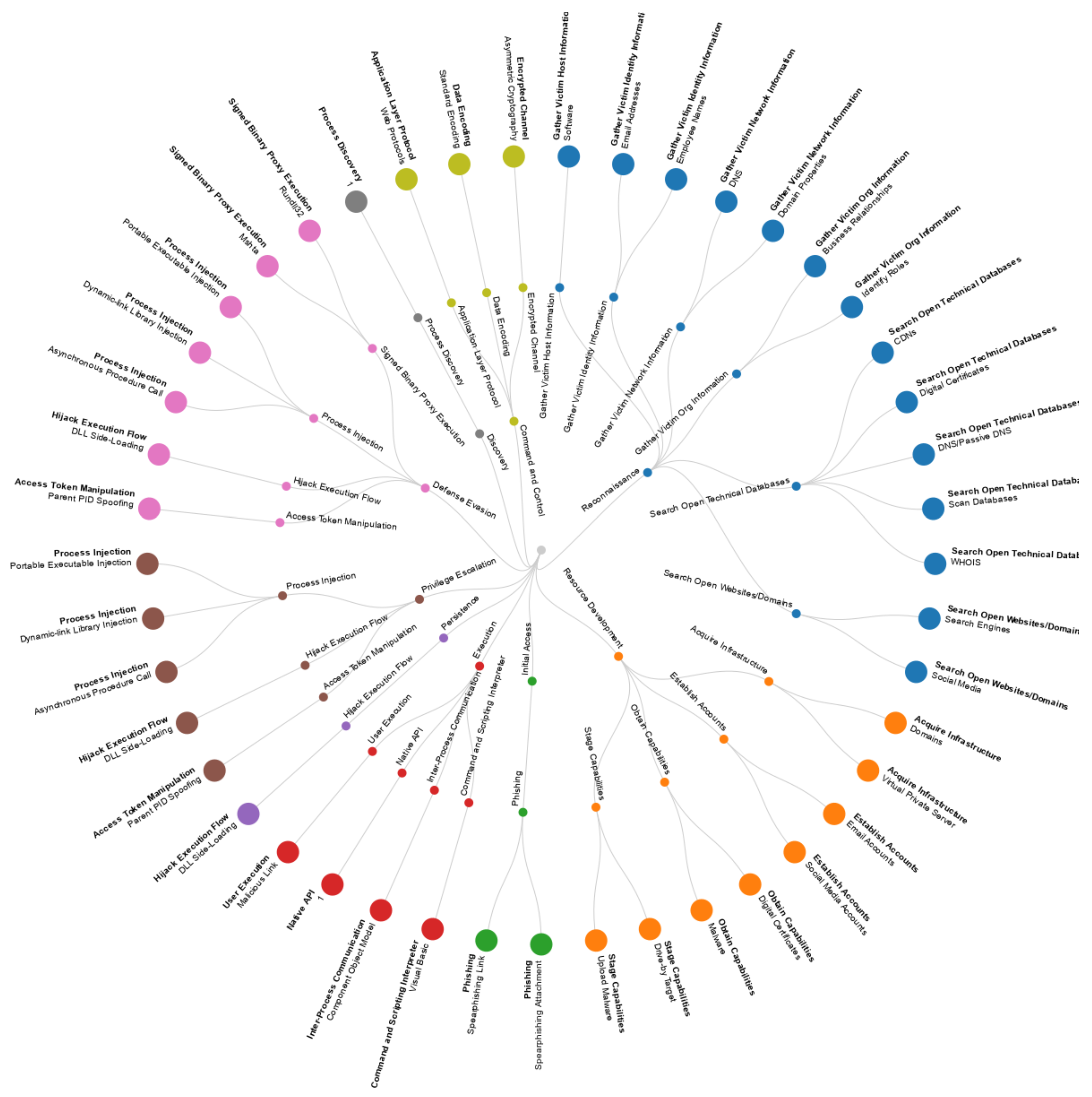
JCP | Free Full-Text | An Empirical Assessment of Endpoint Detection and Response Systems against Advanced Persistent Threats Attack Vectors

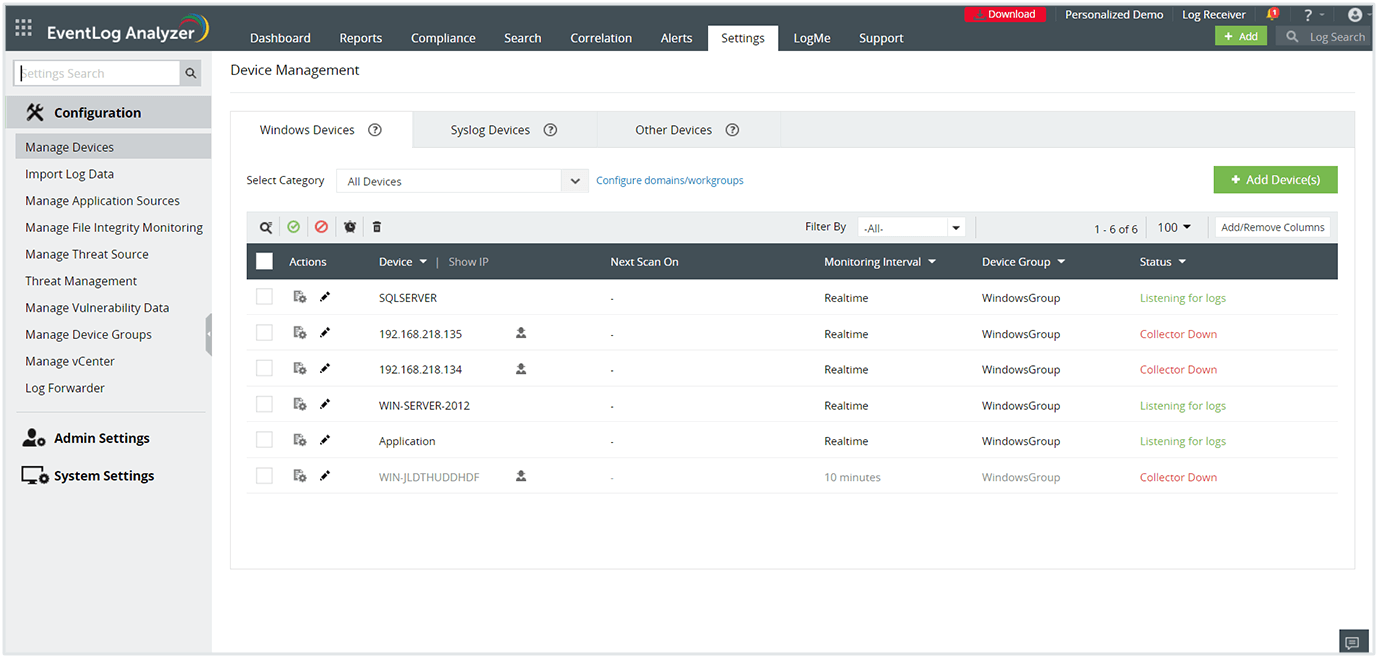
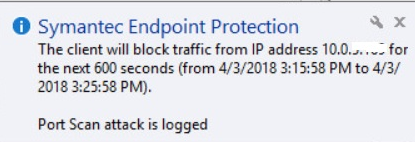
Symantec Endpoint Protection: The client will block traffic from IP address - Step by step with screenshots
![Hybrid rule-based botnet detection approach using machine learning for analysing DNS traffic [PeerJ] Hybrid rule-based botnet detection approach using machine learning for analysing DNS traffic [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2021/cs-640/1/fig-8-full.png)

![SOLVED] Spiceworks being blocked by Symantec (port scan attack) - Spiceworks General Support SOLVED] Spiceworks being blocked by Symantec (port scan attack) - Spiceworks General Support](https://content.spiceworksstatic.com/service.community/p/post_images/0000051389/54504cab/attached_image/Symantec_1.jpg)



![SOLVED] Spiceworks being blocked by Symantec (port scan attack) - Spiceworks General Support SOLVED] Spiceworks being blocked by Symantec (port scan attack) - Spiceworks General Support](https://content.spiceworksstatic.com/service.community/p/post_images/0000054213/54625643/attached_image/Google2.jpg)