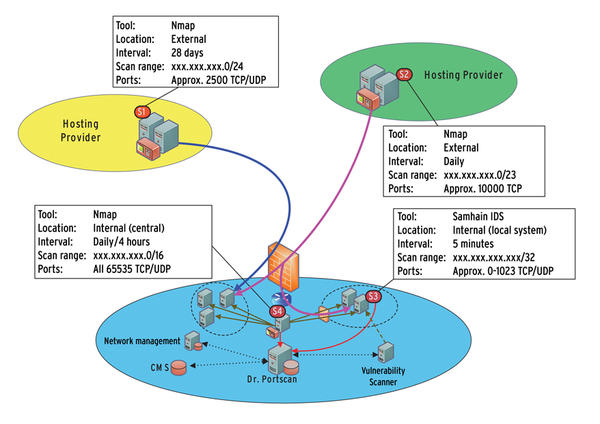
![PDF] Alternative Engine to Detect and Block Port Scan Attacks using Virtual Network Environments | Semantic Scholar PDF] Alternative Engine to Detect and Block Port Scan Attacks using Virtual Network Environments | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1b227ea0f684755183d7c36873c00a853f2e9f73/3-Figure1-1.png)
PDF] Alternative Engine to Detect and Block Port Scan Attacks using Virtual Network Environments | Semantic Scholar

Port scan attack successfully blocked through P4. Fig. 5: Scalability... | Download Scientific Diagram

Deep mining port scans from darknet - Lagraa - 2019 - International Journal of Network Management - Wiley Online Library

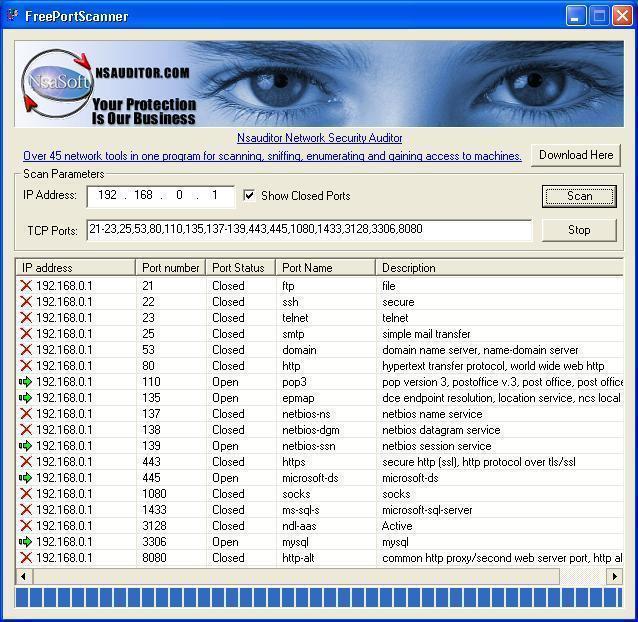





![PDF] Surveying Port Scans and Their Detection Methodologies | Semantic Scholar PDF] Surveying Port Scans and Their Detection Methodologies | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a8ac6c1b1ed25bac14d0f12ff11c9f01fd298d50/3-Figure3-1.png)