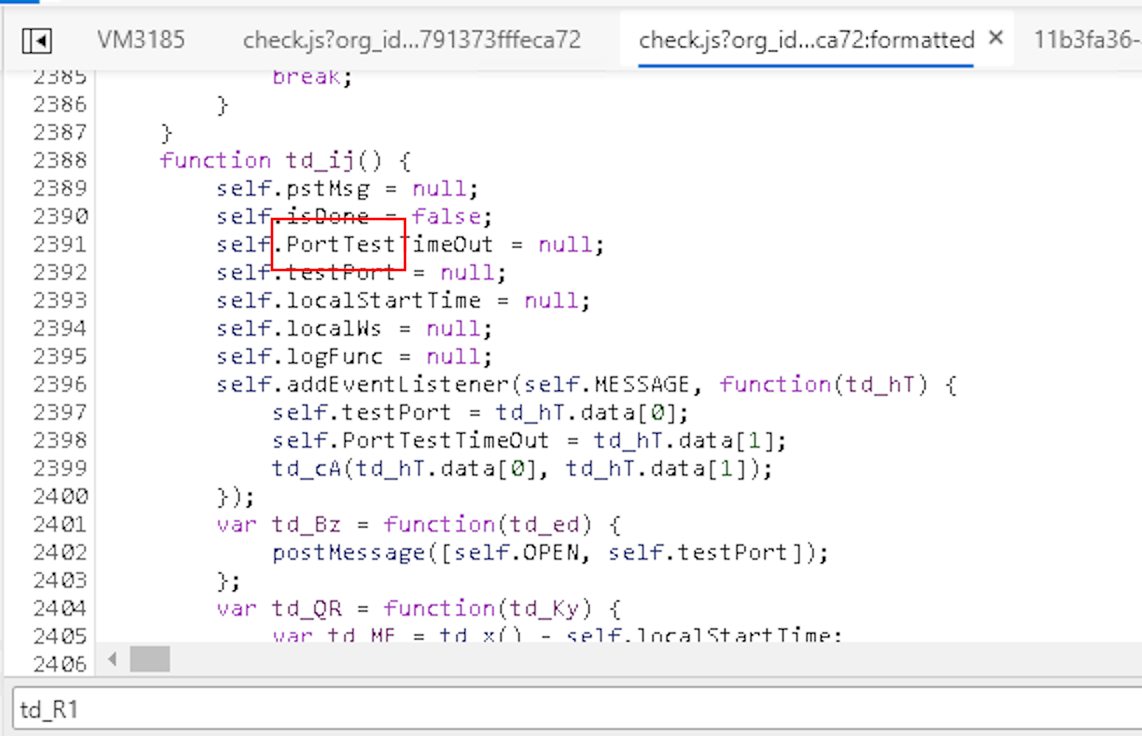
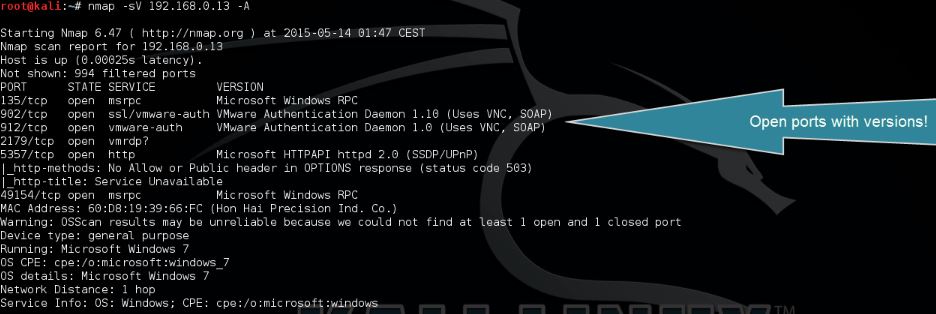
Port Scanning with Nmap (Part 1). Port Scanning is the initial step taken… | by Priya Sharma | Cyversity | Medium

A proposal of port scan detection method based on Packet‐In Messages in OpenFlow networks and its evaluation - Ono - 2021 - International Journal of Network Management - Wiley Online Library
Is port scanning legal? - Latest Hacking News | Cyber Security News, Hacking Tools and Penetration Testing Courses